Discover Agentic AI identities, get access intelligence, ensure human ownership, and enforce governance for autonomous and on-behalf-of agents
The ratio of Agentic-Human Identities to Human Identities
Organizations who had an AI-related breach lacked access controls
Agents are over-privileged
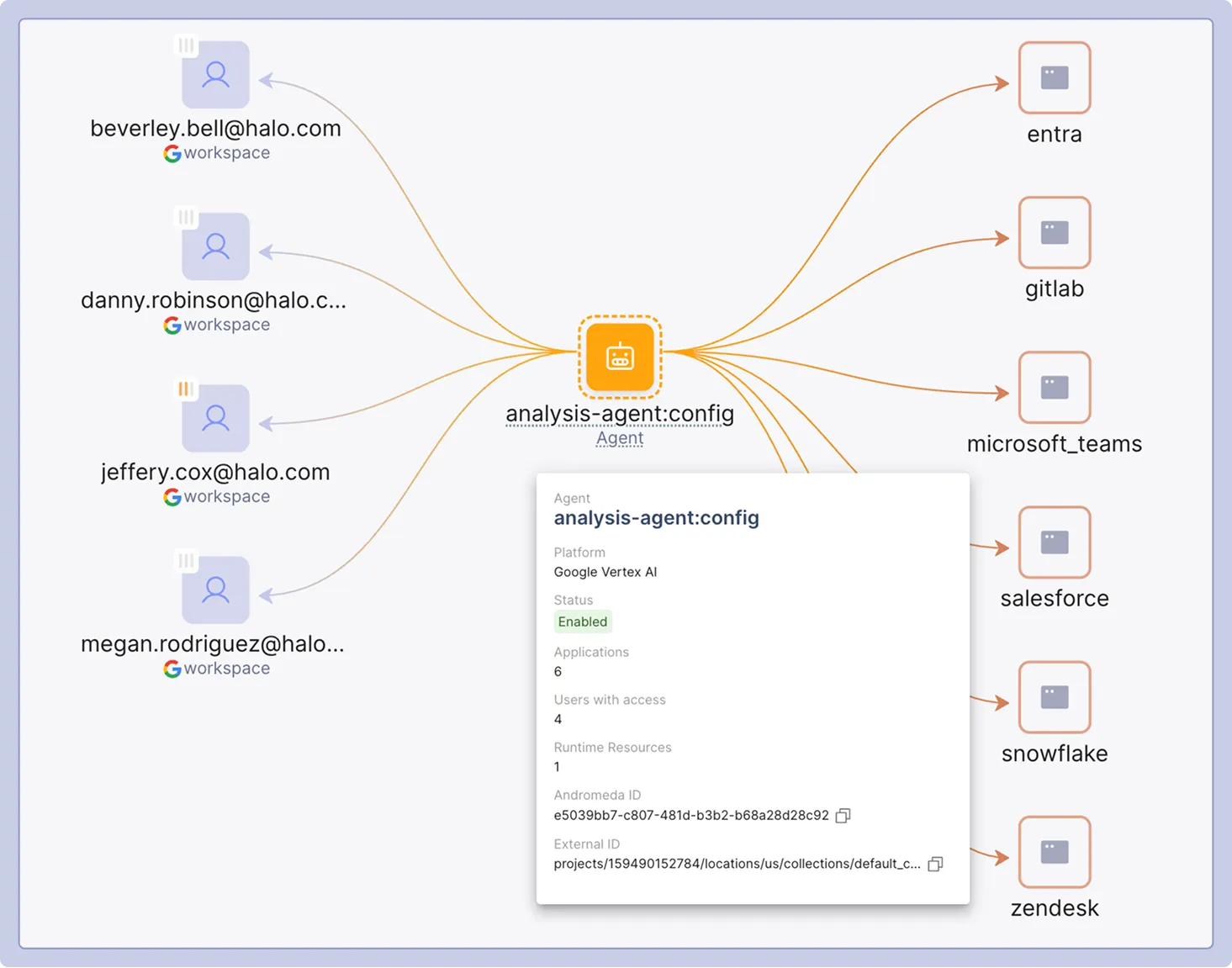
Centralized inventory of all Autonomous and On-Behalf-Of Agents across Enterprise AI platforms
Identify who has access to which Agents and who is using them
Detect what applications Agents can interact with, and what business-critical resources and data they have access to
Everyone wins when Agentic identities are secured and governed alongside human users & NHI



.svg)