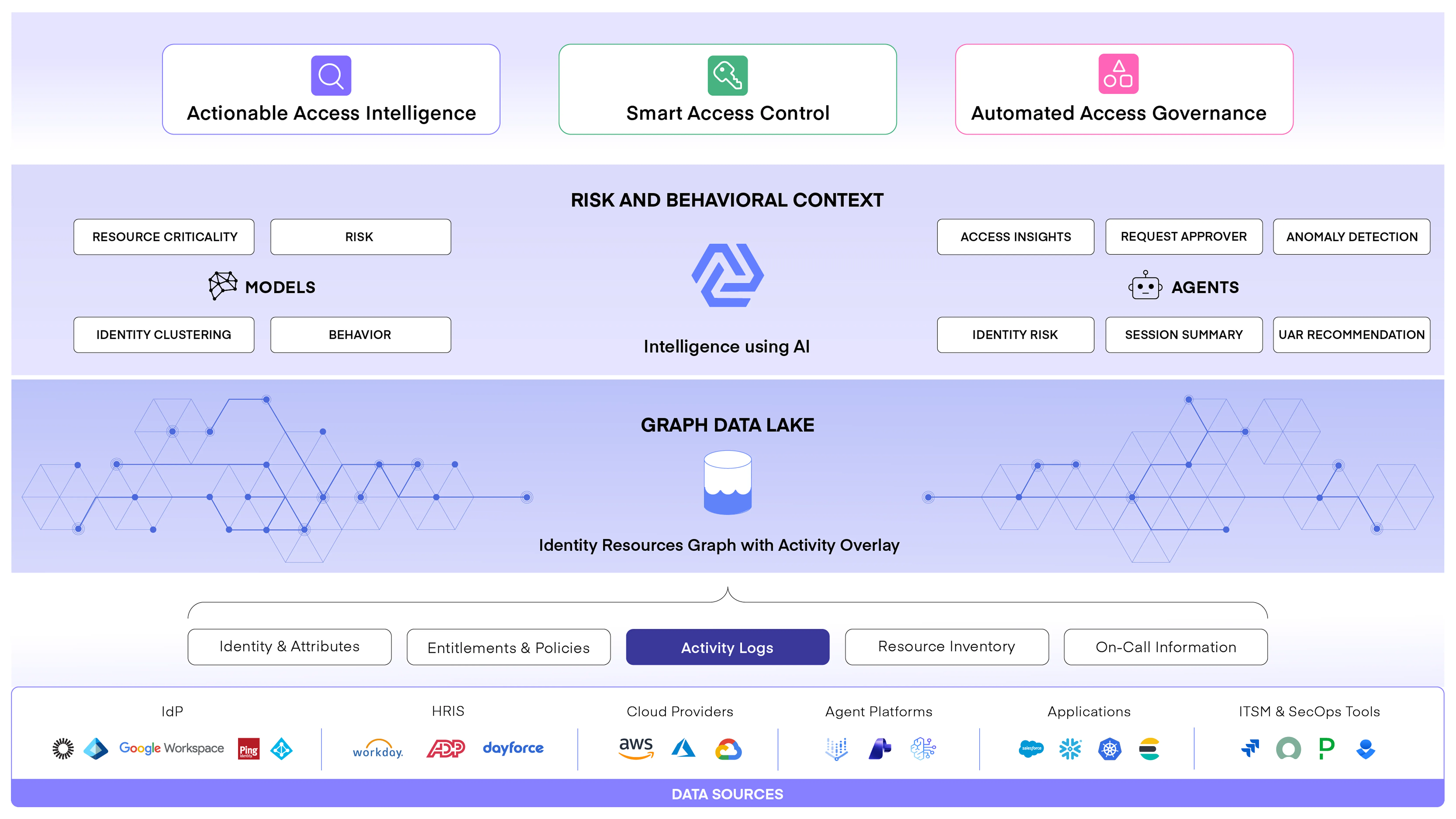
Andromeda is an AI-Powered Identity Security Platform that defends enterprises against identity breaches.
How the Platform works
Identity is the perimeter, and identity breaches are becoming more frequent everyday. When an identity compromise happens, the excessive privilege can have a serious negative impact on your business.
An identity security platform protects your company by helping you achieve and maintain the principle of least privilege through intelligent automation of identity entitlements and lifecycle for both human and non-human identities.




