Beyond the Workflow: Moving to Context-Driven JIT Access

Beyond the Workflow: Moving to Context-Driven JIT Access
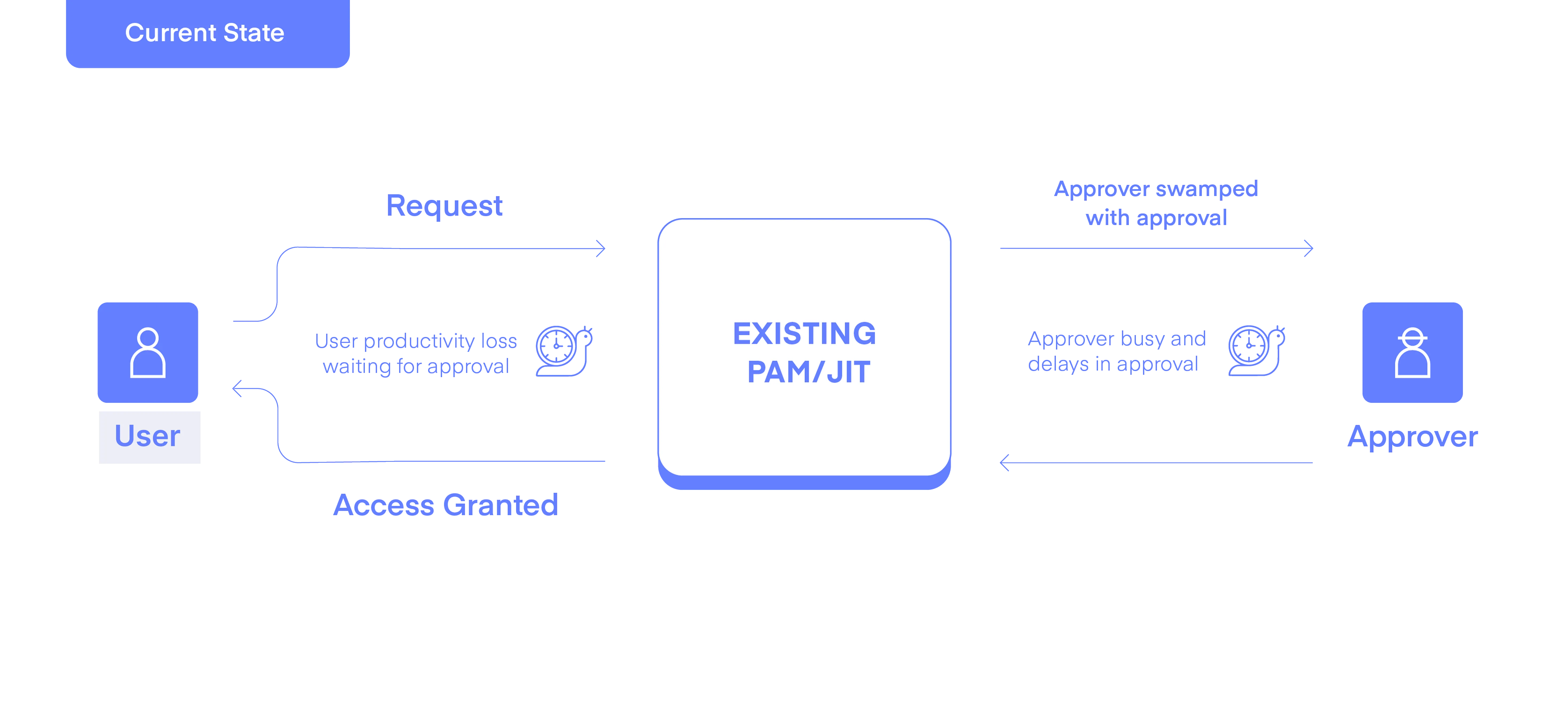
Most Privileged Access Management (PAM) and Just-in-Time (JIT) tools function like digital paperwork. Following a standard workflow, a user submits a request that languishes in an inbox until an approver eventually clicks to “grant” access, triggering provisioning.
While this is better than permanent "standing" privileges, this traditional workflow model creates two major friction points: Productivity Loss for the Requester and an Increased Load on the Approvers.
The Problem with Workflow-Based JIT
The manual approval process has multiple friction points
- Requester Productivity Impact: Users wait anywhere from tens of minutes to hours or days for an approval. They are stalled from performing critical planned activities, which impacts their agility. This leads to "anticipatory requesting" where users ask for access they don’t yet need, just in case, especially when the requester and approvers are in different regions and time zones.
- Approver Overload: Approvers, typically from the security team, asset owners, or managers in Shift Left scenarios, already manage demanding schedules. This process adds a significant administrative burden to their existing responsibilities. In most cases, a request arrives with nothing more than a cryptic 'investigating events' comment, and approvers are flying blind. Without a clear view of the business implications, the request is approved to avoid stalling the requester, turning the process into a "rubber stamp" for audit compliance rather than a security control.
- The Pre-Approval Risk: To prioritize speed, many tools use static policy rules to "pre-approve" requests. (e.g., “Approve john.smith to access the Snowflake sales-data-role during the business hours”). This creates a massive security gap; should an identity be compromised, an attacker can systematically access every resource governed by the static pre-approval rules, completely defeating the purpose of moving to a Just-In-Time system in the first place.
Andromeda: Context-Driven Automation
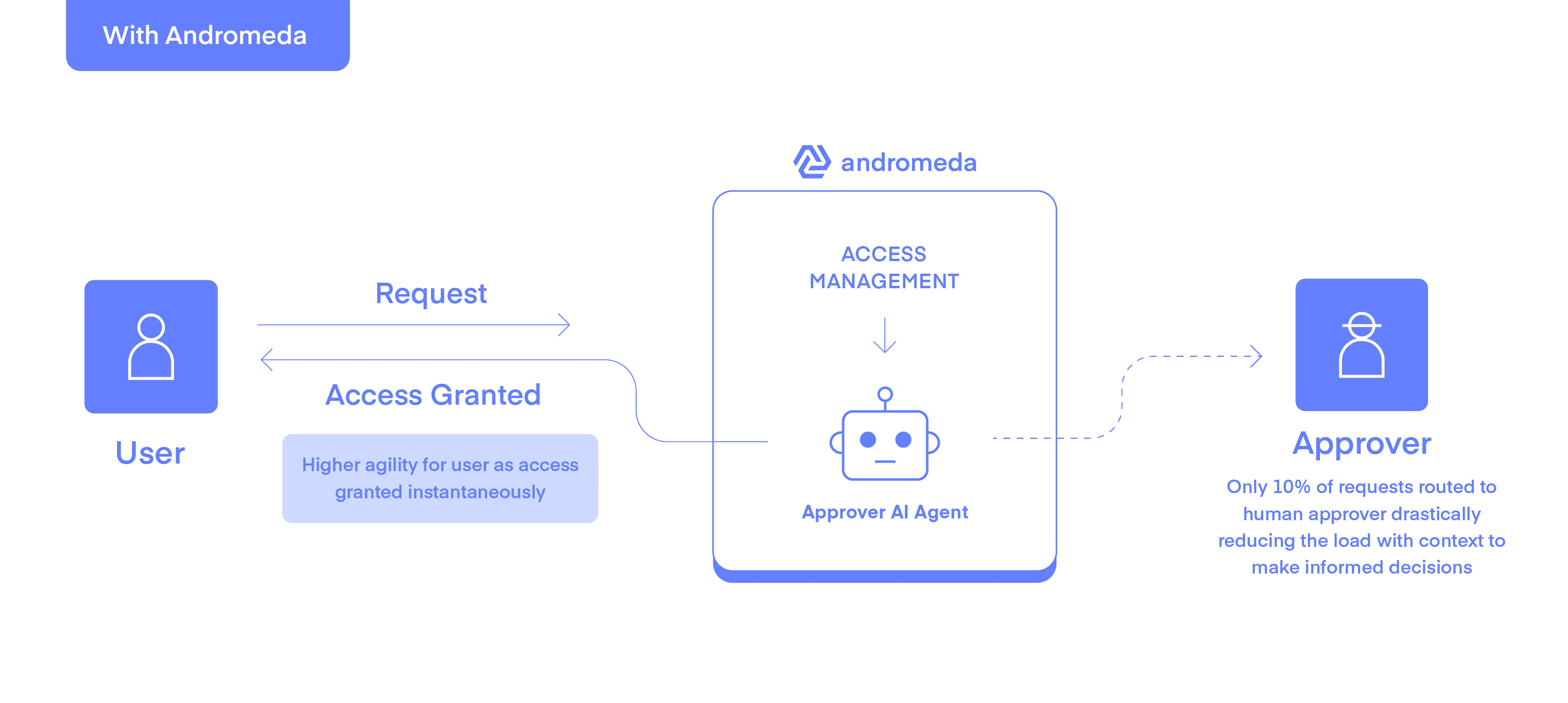
Andromeda shifts the focus from manual checklists to Dynamic Context-Driven Automation.
A request is analyzed by an Approver-AI-Agent, and if it aligns with a ‘paved path’ it skips the human approver and grants the request automatically. The user gets access instantaneously. The Agent operates 24/7, analyzing all requests across multiple dimensions to make context-driven decisions. With one dedicated task, the Agent removes the human bottleneck by automatically analyzing and approving only ‘safe’ requests, sending risky or policy-violating requests for human review.
Analysis Performed by the Andromeda AI-Approver Agent
To decide if a request is safe, the Agent analyzes a combination of internal behavior models and external signals:
Intelligent Escalation
When the Approver-Agent’s confidence level is low—meaning it cannot verify the context, the risk of the requested access is too high, or there is a failure in some of the context signals—it doesn't just reject the request. It routes the request to an approver with a full contextual briefing, providing the specific reasons for the flag. For example:
"The user is requesting access from a new Geo, and the request time is not typical for this user. Furthermore, this is the 3rd request by this user in the last 5 minutes, having requested 3 different types of access back-to-back."
Approvers are no longer flooded with routine notifications, because the Agent handles the vast majority of safe, "paved-path" requests automatically. Only a small subset of high-risk requests are sent to the human approver, dramatically reducing the administrative overhead associated with manual approvals. This allows the approvers to ignore the noise and make fast, informed, data-driven decisions on the events that actually matter.
Impact: Agility Meets Security
By combining Dynamic Context with External Signals, Andromeda allows organizations to move beyond the limitations of existing, workflow-based JIT. The results are measurable:
- Zero Impact on Productivity: Because the Agent approves most requests, requesters receive the access they need instantaneously in most cases. Engineers and business users can remain agile and focused on their work, rather than waiting for requested access.
- Drastic Attack Surface Reduction: By moving from permanent "standing" access to JIT, you ensure that high-risk permissions only exist when there is a verified business need. This eliminates the window of opportunity for attackers to move laterally using idle privileges.
- Optimized Security Oversight: Only outlier requests—those that truly pose a risk—are routed to a human approver, reducing administrative overhead and preventing "approval fatigue." When a human is needed, they have the full context of what they need to pay attention to in front of them to make a high-stakes accept or reject decision, securely and quickly.
Andromeda continues to expand both the internal dynamic context and the external signals, e.g., with upcoming integrations into XDR tools (Crowdstrike and Microsoft Defender) to include real-time user and device posture in the Agent’s decision-making process.
Our mission is to ensure Just-in-Time Access is secure and frictionless to improve user productivity and operational efficiency to accelerate the business.
Beyond the Workflow: Moving to Context-Driven JIT Access
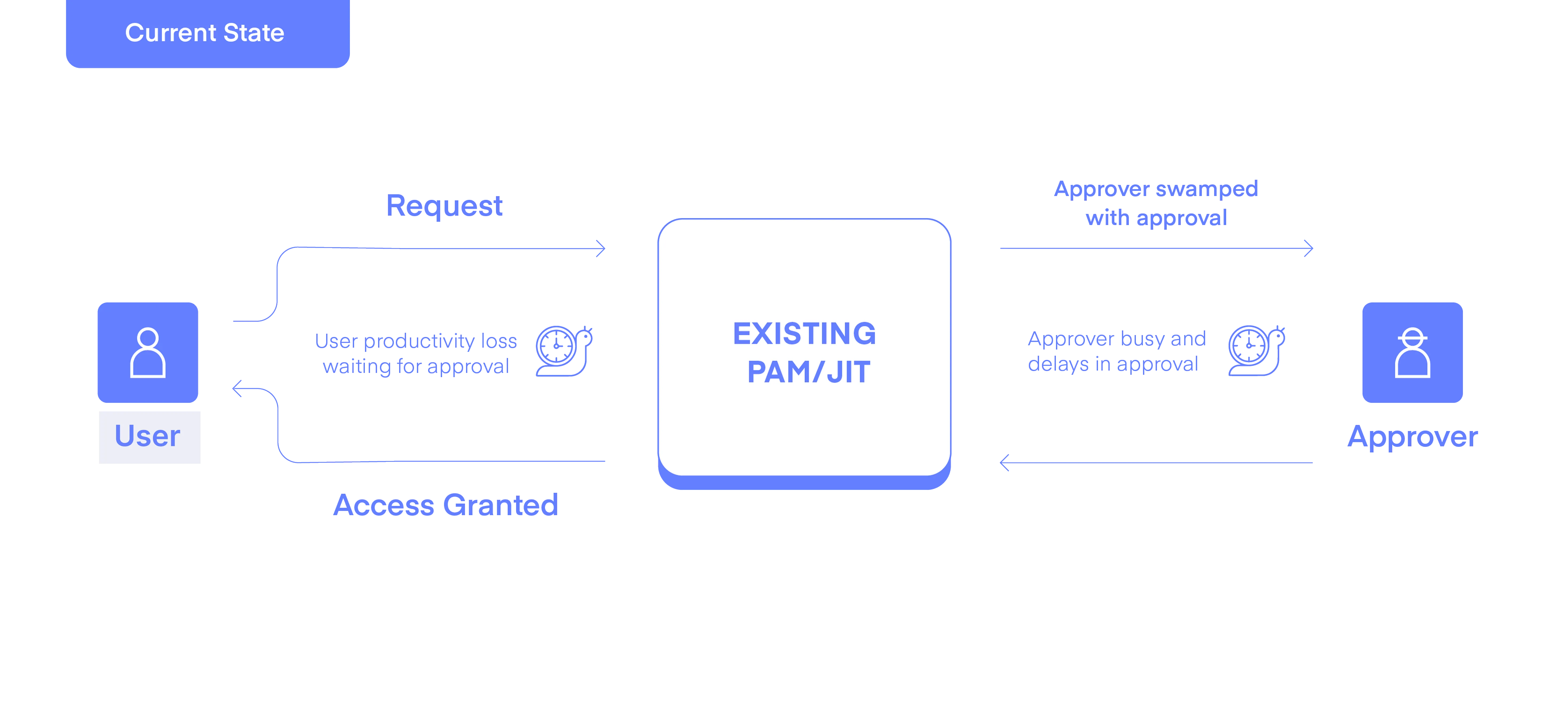
Most Privileged Access Management (PAM) and Just-in-Time (JIT) tools function like digital paperwork. Following a standard workflow, a user submits a request that languishes in an inbox until an approver eventually clicks to “grant” access, triggering provisioning.
While this is better than permanent "standing" privileges, this traditional workflow model creates two major friction points: Productivity Loss for the Requester and an Increased Load on the Approvers.
The Problem with Workflow-Based JIT
The manual approval process has multiple friction points
- Requester Productivity Impact: Users wait anywhere from tens of minutes to hours or days for an approval. They are stalled from performing critical planned activities, which impacts their agility. This leads to "anticipatory requesting" where users ask for access they don’t yet need, just in case, especially when the requester and approvers are in different regions and time zones.
- Approver Overload: Approvers, typically from the security team, asset owners, or managers in Shift Left scenarios, already manage demanding schedules. This process adds a significant administrative burden to their existing responsibilities. In most cases, a request arrives with nothing more than a cryptic 'investigating events' comment, and approvers are flying blind. Without a clear view of the business implications, the request is approved to avoid stalling the requester, turning the process into a "rubber stamp" for audit compliance rather than a security control.
- The Pre-Approval Risk: To prioritize speed, many tools use static policy rules to "pre-approve" requests. (e.g., “Approve john.smith to access the Snowflake sales-data-role during the business hours”). This creates a massive security gap; should an identity be compromised, an attacker can systematically access every resource governed by the static pre-approval rules, completely defeating the purpose of moving to a Just-In-Time system in the first place.
Andromeda: Context-Driven Automation
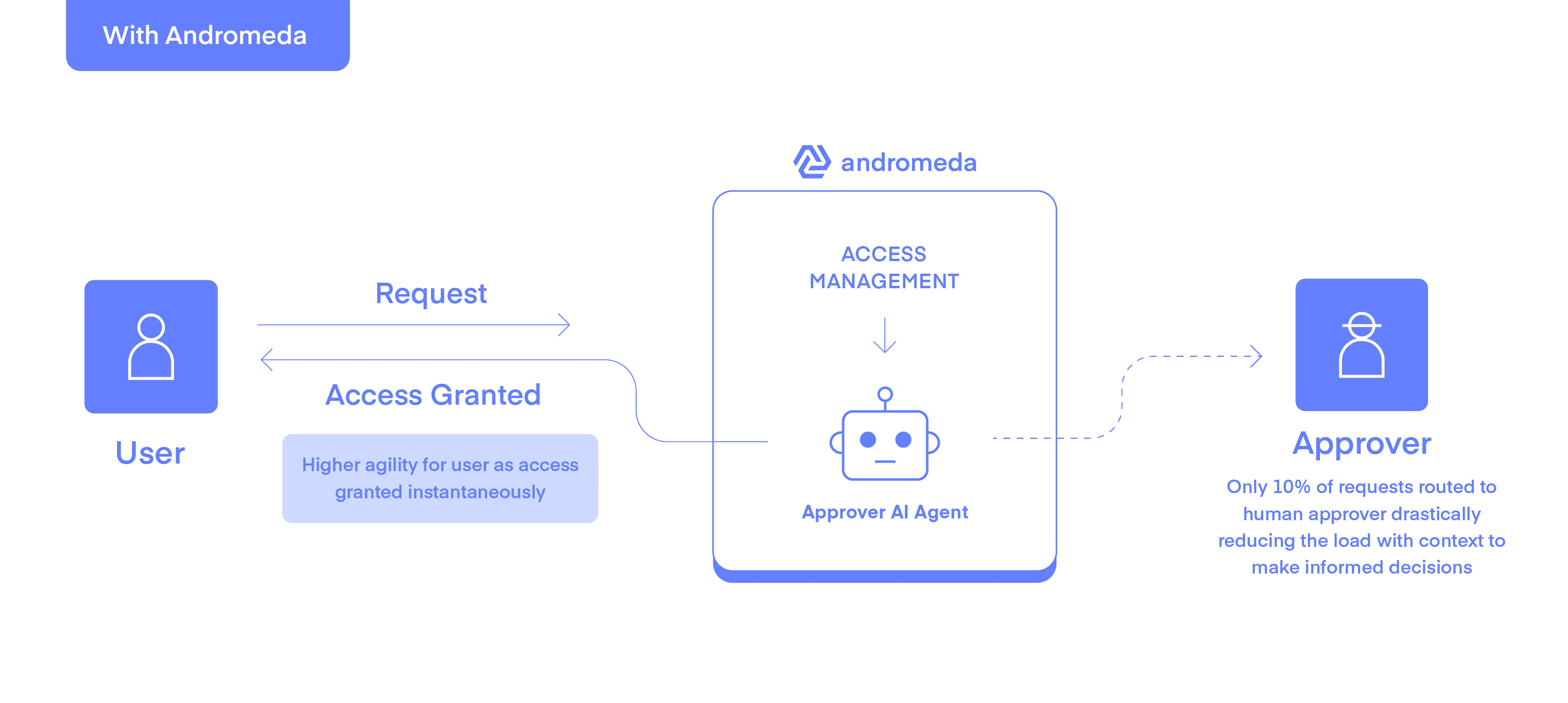
Andromeda shifts the focus from manual checklists to Dynamic Context-Driven Automation.
A request is analyzed by an Approver-AI-Agent, and if it aligns with a ‘paved path’ it skips the human approver and grants the request automatically. The user gets access instantaneously. The Agent operates 24/7, analyzing all requests across multiple dimensions to make context-driven decisions. With one dedicated task, the Agent removes the human bottleneck by automatically analyzing and approving only ‘safe’ requests, sending risky or policy-violating requests for human review.
Analysis Performed by the Andromeda AI-Approver Agent
To decide if a request is safe, the Agent analyzes a combination of internal behavior models and external signals:
Intelligent Escalation
When the Approver-Agent’s confidence level is low—meaning it cannot verify the context, the risk of the requested access is too high, or there is a failure in some of the context signals—it doesn't just reject the request. It routes the request to an approver with a full contextual briefing, providing the specific reasons for the flag. For example:
"The user is requesting access from a new Geo, and the request time is not typical for this user. Furthermore, this is the 3rd request by this user in the last 5 minutes, having requested 3 different types of access back-to-back."
Approvers are no longer flooded with routine notifications, because the Agent handles the vast majority of safe, "paved-path" requests automatically. Only a small subset of high-risk requests are sent to the human approver, dramatically reducing the administrative overhead associated with manual approvals. This allows the approvers to ignore the noise and make fast, informed, data-driven decisions on the events that actually matter.
Impact: Agility Meets Security
By combining Dynamic Context with External Signals, Andromeda allows organizations to move beyond the limitations of existing, workflow-based JIT. The results are measurable:
- Zero Impact on Productivity: Because the Agent approves most requests, requesters receive the access they need instantaneously in most cases. Engineers and business users can remain agile and focused on their work, rather than waiting for requested access.
- Drastic Attack Surface Reduction: By moving from permanent "standing" access to JIT, you ensure that high-risk permissions only exist when there is a verified business need. This eliminates the window of opportunity for attackers to move laterally using idle privileges.
- Optimized Security Oversight: Only outlier requests—those that truly pose a risk—are routed to a human approver, reducing administrative overhead and preventing "approval fatigue." When a human is needed, they have the full context of what they need to pay attention to in front of them to make a high-stakes accept or reject decision, securely and quickly.
Andromeda continues to expand both the internal dynamic context and the external signals, e.g., with upcoming integrations into XDR tools (Crowdstrike and Microsoft Defender) to include real-time user and device posture in the Agent’s decision-making process.
Our mission is to ensure Just-in-Time Access is secure and frictionless to improve user productivity and operational efficiency to accelerate the business.
